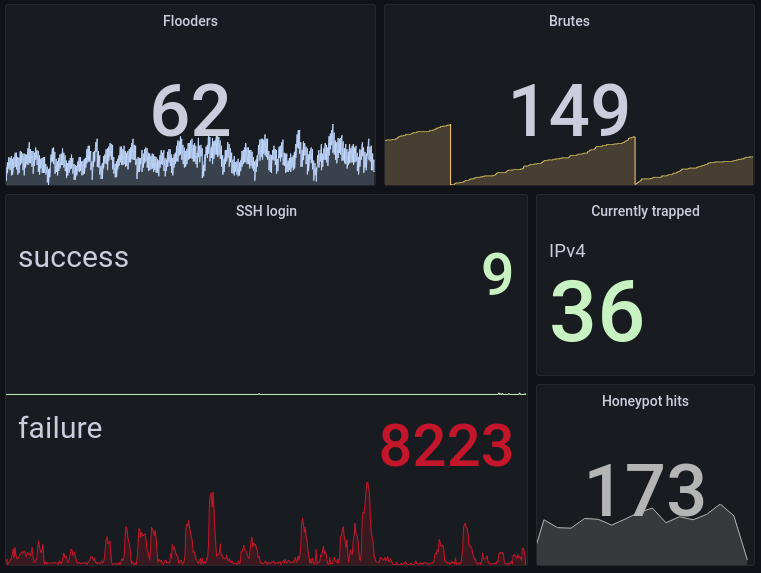
In the past two weeks I set up a new VPS, and I run a small experiment. I share the results for those who are curious.
Consider that this is a backup server only, meaning that there is no outgoing traffic unless a backup is actually to be recovered, or as we will see, because of sshd.
I initially left the standard “port 22 open to the world” for 4-5 days, I then moved sshd to a different port (still open to the whole world), and finally I closed everything and turned on tailscale. You find a visualization of the resulting egress traffic in the image. Different colors are different areas of the world. Ignore the orange spikes which were my own ssh connections to set up stuff.
Main points:
-
there were about 10 Mb of egress per day due just to sshd answering to scanners. Not to mention the cluttering of access logs.
-
moving to a non standard port is reasonably sufficient to avoid traffic and log cluttering even without IP restrictions
-
Tailscale causes a bit of traffic, negligible of course, but continuous.
I get what you say, and you’re definitely not wrong to do it. But as I see it, you only saved ~80Kib of ingress and a few lines of logs in the end. From my monitoring I get ~5000 failed auth per day, which account for less than 1Mbps average bandwidth for the day.
It’s not like it’s consuming my 1Gbps bandwidth or threatening me as I enforce ssh key login. I like to keep things simple, and ssh on port 22 over internet makes it easy to access my boxes from anywhere.
ssh -p 12345 would leave your boxes accessible from anywhere too. Other blocks of IPs receive 10 times or more requests, as scanners can focus on blocks of ips from major providers.
Yeah I know, I just don’t really care about that traffic to bother changing it :) Also, I’m talking about a server hosted on Hetzner, so I feel like it’s scanned a lot.
I don’t get why people leave interfaces the public doesn’t need access to open to the public – especially SSH.
Use a VPN if you need access to those interfaces from the “outside”. They’re stupidly easy to set up these days, particularly with Wireguard.
A VPN is easy to setup (and I have it setup by the way), but no VPN is even easier. SSH by itself is sufficiently secure if you keep it up to date with a sane configuration. Bots poking at my ssh port is not something that bother me at all, and not part of any attack vector I want to be secure against.
Out of all the services I expose to the clear web, SSH is probably the one I trust the most.
I would generally agree with this a strong password and SSH without keys has never gone sideways for me and over 15 years of having public Linux servers. but I also make sure to install all security updates on a regular basis on any server no matter what SSH configuration is.
Agreed ! Also it would make graphs pretty boring ;)
Defense in depth – maybe I’m paranoid, but just because something is unlikely doesn’t mean an extra layer of security isn’t advantageous. Particularly when I already have a VPN, so there’s little reason not to use it.
Plus, my logs are easily checked as a side effect.
To each their own ! Security is a complex topic which usually resolves to adjusting the “security/annoyance” cursor to the best position.
In my case the constraints of using a VPN simply outweighs the security benefits.
I’ll take that tiny amount of traffic telling scanners there’s no password auth over having to remember port settings for ssh, scp and rsync any day.
My configs remember stuff for me.
For me it’s not about the traffic, more the log spam.
Generally I’ll have :22 enabled internally, and anything non-standard is defined in
~/.ssh/configand shared out so I don’t have to remember things.vim ~/.ssh/configYeah, but how do you close VIM then? Restarting the computer takes some time!!!111
Checkmate!!
Fair point. These logs are only useless chatter anyway for everyone with proper key auth.
I don’t know if it was mentioned already but how could I check if my ports are under “attack”? OPs graphic looks really nice
Hi, to check attacks you should look at the logs. In this case auth.log. Being attacked on port 22 is not surprising neither really troublesome if you connect via key pair.
My graph was showing egress traffic, on any kind of server the traffic due to these attacks would have been invisible but on a backup server which has (hopefully) only ingress you can clearly see the volume of connections from attackers from bytes teansmitted
Exploring Go High Level:
What’s the Enthusiasm About?
Hello there! Are you familiar with Go High Level? If not, let’s break it down. Imagine managing multiple apps for marketing. Sounds busy. That’s where Go High Level comes in. It’s like that friend who has a solution for everything. Whether you are working on creating an outstanding sales funnel or sending out an email campaign, this platform has your back. The best part? They let you test drive everything with a 14-day free trial. It’s like trying out a new car but for your business. And if you ever need assistance, their support team is just a click away. Pretty exciting, huh?So, How Much Does It Cost?
Alright, let’s talk about the financial side. Go High Level offers 3 main plans. The Agency Starter Plan is perfect if you’re just starting or have a small business. It’s loaded with all the essential tools, and it’s quite cost-effective. But if you’re looking to scale up, the Agency Unlimited Plan is your best choice. It’s like the VIP pass at a concert, giving you access to everything without any limitations. Not sure about committing? Remember that 14-day free trial I mentioned? It’s a great way to give it a try without any obligations. Lastly, they offer a Pro plan that includes “SaaS mode,” where you can white label the product under your brand. Fantastic!Why Everyone’s Raving About It:
In a world full of sophisticated digital tools, Go High Level is like that all-in-one Swiss Army knife. There’s no need to switch between apps because it has everything under one roof. Whether you’re a newcomer or an experienced marketer, it’s super user-friendly. It’s not just about launching impressive campaigns; they ensure you understand their performance with top-notch analytics. There’s even a white-label feature for marketing agencies, so you can add your brand and impress your clients.Here is a link to their 14-day free trial:
https://www.gohighlevel.com/?fp_ref=get-started-now.Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters DNS Domain Name Service/System HTTP Hypertext Transfer Protocol, the Web IP Internet Protocol SSH Secure Shell for remote terminal access UDP User Datagram Protocol, for real-time communications VPN Virtual Private Network VPS Virtual Private Server (opposed to shared hosting) nginx Popular HTTP server
7 acronyms in this thread; the most compressed thread commented on today has 8 acronyms.
[Thread #42 for this sub, first seen 14th Aug 2023, 15:55] [FAQ] [Full list] [Contact] [Source code]
Good bot!
Public key auth, and fail2ban on an extremely strict mode with scaling bantime works well enough for me to leave 22 open.
Fail2ban will ban people for even checking if the port is open.
If Fail2Ban is so important, why the h*** does it not come installed and enabled as standard?!
Security is the number-1 priority for any OS, and yet stock SSHD apparently does not have Fail2Ban-level security built in. My conclusion is that Fail2Ban cannot therefore be that vital.
Honest question, is there a good default config available somewhere or is what
apt install fail2bandoes good to go? All the tutorials I’ve found have left it to the reader to configure their own rules.Yeah fail2ban has worked great for me
You really shouldn’t have something kike SSHD open to the world, that’s just an unnecessary atrack surface. Instead, run a VPN on the server (or even one for a network if you have several servers on one subnet), connect to that then ssh to your server. The advantage is that a well setup VPN simply won’t respond to an invalid connection, and to an attacker, looks just like the firewall dropping the packet. Wireguard is good for this, and easy to configure. OpenVPN is pretty solid too.
I usually just run a ZeroTier client on my Pi connected to a private P2P network to solve this issue, and then have ProtonVPN over Wireguard for all internet traffic in and out of the Pi.
You say this and are downvoted.
While we are coming off the tail of Def Con where there where a plethora or small talks and live examples of taking advantage and abusing just this.
Just trying to parse your comment, I assume your first “this” and second “this” are referring to different things, right?
I don’t understand your comment, what you are saying. Could you elaborate a bit, please? I’m interested why it’s a bad idea what previous comment suggested.
Of course I can dig into DefCon videos and probably would do if needed, but perhaps you know what exactly the issue is
The first this means the comment he answered to and the second one means ssh being used as an attack surface, being described in defCon talks
ITT: People who don’t understand Tailscale or are allergic to it for ‘reasons’
Is public key authentication not good enough? Tailscale is cool but can be tedious if you also use other VPNs
Yeah that’s what I have too. One of my servers is exposed with key auth and I just tunnel to other servers from there. A few MB egress is nothing compared with the amount of spam my webserver needs to deal with
I am not in IT, what does this mean ?
Computers communicate across networks using ports. Port 22 is a commonly used remote administration port called ssh. Bots go around probing computers with an open port 22 hoping to find badly secured or outside misconfigured ssh servers to turn them into bots and crypto miners, etc.
Its crazy people can do all these stuff. I can’t even edit my word document. Being said that I want to learn IT but looks hell stressful for $100-$200k job. I was in content & marketing making $130k and we used to discuss about shades of color to use in a font for 3-4 weeks. Its crazy how you guys have to fix issues within minutes on those tickets. The more i learn about IT, I feel like I should stay away from it.
Not everyone in IT needs to fix tickets or work in a high-stress environment. In one of my previous roles, I was a projects engineer, and I was basically given a bunch of projects to work on (like there was a small python-based project - they needed to automate something; then there was one to get them into a hybrid cloud setup; another project to upgrade something and so on). I didn’t really have any break-fix tickets to work on, although I was occasionally asked if I could help, when there was some spare time or if it was something high-level the ops guys couldn’t fix. Basically a total chill job, I was free to allocate time on my projects as I saw fit, no hard deadlines, no SLAs to meet, and the best part - no users to deal with.
Of course, it wasn’t always like this. To get here, I had to do those grunt roles first, those stressful jobs with tickets that needed to be fixed in minutes, dealing with angry users and stuff. But thankfully my career has progressed past that stage now.
One of the sad aspects of my job (in IT) is building tools to eliminate less stressful jobs, especially ones that pay well (usually management or accounting, in my case). Design has definitely been a specific target in recent years though – off the top of my head I could at least imagine two approaches to writing a tool that automates color and font selection with results comparable to human expertise.
This is one reason it’s a good idea to regularly study new things (IT or otherwise). I have to retool every few years as whatever I know becomes obsolete – this used to mainly be a frustration in IT, but is rapidly becoming a necessary process in other fields. It won’t be necessary to become an IT expert, but I would keep up-to-date on how to use the new tools technology provides… especially if I wanted to keep a job in say, graphics design or copywriting!
(Incidentally, my first job in this country was in marketing! It was high-stress and I did not earn 130k. I recall font and color choice processes vividly :D)
Yea dont create anything bro. 100k-200k is nothing in 2023. Like you can’t even afford a decent house for a family. I do my 9-5 with the least work possible and go home. Tried starting a business but failed miserably so back to 9-5.
Yeah… I couldn’t cope with that unfortunately (I’m a bit jealous, it sounds nice). I need to work long hours and make things, it’s a compulsion. “Taking it easy” can stress me out to the point where I end up in a hospital.
So I sold all my worldly possessions and immigrated to the developing world on an investment visa (where things are made). My timing was a few years early, but I had no path to a decent life left except having my own company in a growth economy – my entire industry vanished twice overnight in my home country due to changes in legislation.
Nowadays, looking at the local economy, there is no path to home ownership except for people who own companies, and maybe senior executives or senior software engineers. An average university-educated couple would have to save 100% of their income for their entire adult life to afford a nice home – if they don’t have kids. I think this kind of cruel equation is slowly coming to the West too – although you guys have more land so I guess it takes longer.
Feel for you brother. Dont get dominated by stupid 9-5 managers, directors, CEO instead try dominating them. They cant do all thr work by themselves , even if they fire you, its a 9-5 job. You have to take what’s yours legally or illegally. Look at the history from colonization to new era Capitalism. More power to you bro!
Perhaps ironically, I live in a nominally Communist country that went through decolonization quite a number of times. It doesn’t change much in my daily life (I’m not really political), although I arguably own some tiny slice of the means of production these days. So maybe in retirement I’ll provide public access to those for working class people. That would be really fun, I think. Who knows what we might create together? Certainly if the machines are sitting unused in my retirement, they are creating nothing, and I would feel sad for the machines.
I don’t do the whole 9-5 thing. That would stress me out! I work as long as I feel like, any day of the week I feel like. Generally, this is really nice for both managing stress (there’s always tomorrow!) and steamrolling over any competition.
I’m just a mercenary (and a bureaucrat) though. You pay my fee in filthy lucre, and the job gets done – legally, and reliably. If someone annoys me with politics at a client, I just try and replace them with a computer program. The result is that several of my best coworkers are machines these days. I foresee that trend increasing with time.
I can’t edit Word documents for shit lol. I edit everything using Markdown (the same formatting used here) because I don’t have to think about it.
That said every job can get stressful now and again, and this line of work is no different, but most days it’s just work. Make this change, make this thing do something else, kill this thing that’s costing money and everyone stopped using last year without telling anyone, etc. Typical things.
Exploring Go High Level:
-
What’s the Enthusiasm About?
Hello there! Are you familiar with Go High Level? If not, let’s break it down. Imagine managing multiple apps for marketing. Sounds busy. That’s where Go High Level comes in. It’s like that friend who has a solution for everything. Whether you are working on creating an outstanding sales funnel or sending out an email campaign, this platform has your back. The best part? They let you test drive everything with a 14-day free trial. It’s like trying out a new car but for your business. And if you ever need assistance, their support team is just a click away. Pretty exciting, huh? -
So, How Much Does It Cost?
Alright, let’s talk about the financial side. Go High Level offers 3 main plans. The Agency Starter Plan is perfect if you’re just starting or have a small business. It’s loaded with all the essential tools, and it’s quite cost-effective. But if you’re looking to scale up, the Agency Unlimited Plan is your best choice. It’s like the VIP pass at a concert, giving you access to everything without any limitations. Not sure about committing? Remember that 14-day free trial I mentioned? It’s a great way to give it a try without any obligations. Lastly, they offer a Pro plan that includes “SaaS mode,” where you can white label the product under your brand. Fantastic! -
Why Everyone’s Raving About It:
In a world full of sophisticated digital tools, Go High Level is like that all-in-one Swiss Army knife. There’s no need to switch between apps because it has everything under one roof. Whether you’re a newcomer or an experienced marketer, it’s super user-friendly. It’s not just about launching impressive campaigns; they ensure you understand their performance with top-notch analytics. There’s even a white-label feature for marketing agencies, so you can add your brand and impress your clients.
Here is a link to their 14-day free trial:
https://www.gohighlevel.com/?fp_ref=get-started-now.-
And yet it is more likely that tailscale get owned since the reward is much higher. I take my chances with my secured openssh server at port 22 vs a 3rd party company who controlls the access.
Just setup a wireguard system that’s pretty bulletproof
So is SSH
Wireguard doesn’t respond but I agree open-ssh is pretty solid. Can’t speak for any of the other ssh implementations. It can also be poorly configured. Like you could use a password
The benefit of Wireguard is that if you screw it up, it just won’t work. It basically enforces security.
Well, unless you tried to use the original PFSense module.
Or, you know, just use key auth only and fail2ban. Putting sshd behind another port only buys you a little time.
I’ve noticed that a lot of the scans these days almost always switch IPs after 2-3 attempts, making IP blocking a lot more difficult.
Let’s say that you could ban for an indefinitely large amount of time after a single failure to authenticate, that’d make them run out of IPs much quicker than you’d run out of CPU/BW, so I don’t really see the issue
Potentially yeah, although a single failure means I might lock myself out by accident.
True, but very unlikely (once your ssh client is configured once and for all), and in that event you can always switch connection (use a data network, proxy, vpn, hop from another server you have ssh access, etc)
Yeah but the majority of bots out there are going after easy prey. Honestly, if you use public key authentication with ssh you should be fine, even if it is on port 22. But it does of course clog up access logs.
The majority of bots out there are stopped by just using a hard to guess password. It’s not them that you should be worried about.
The majority of bots doesn’t even show up in the logs if you disable password auth in the server config, as you typically should.
As others have already said, set up a VPN like wireguard, connect to the VPN and then SSH to the server. No need to open ports for SSH.
I do have port 22 open on my network, but it’s forwarded to an SSH tarpit: https://github.com/skeeto/endlessh
Throw CrowdSec on there to stop the bots before they can do anything